Russia is revealed as the prime actor in attacks on the 2018 Winter Games
It has recently been revealed that Russian cyberwarriors targeted the 2018 Winter Olympics in South Korea and have apparently been foiled in their attempts to wreck the postponed Tokyo Summer Olympics.
In 2018, networks around the Games were taken out, the Web site went down, and it proved impossible to print tickets. Originally, the malware injected into the Olympic sites was believed to be of Chinese origin. At the time, the attack vector was unknown, but its MO was to steal passwords from the Windows Registry and from Web browsers, and to make its way through the network, securely deleting files in a way that made them unrecoverable.
Later analysis seems to show that the parties originally blamed for this, the Chinese and North Koreans, were in fact innocent of this particular attack, named ‘Olympic Destroyer’. Although metadata contained in the data wiping portion of the software initially seemed to be identical to that used in the cyberheist against the Central Bank of Bangladesh in 2017, Bluenoroff, which netted $81m, more detailed examination showed that it had been developed in a different environment and had been disguised to conceal the fact that it was from a different source.
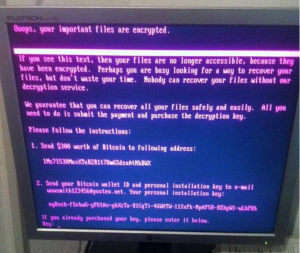
In October 2020, the true culprits were revealed – Russian military hackers, specifically those forming a team in a part of the Russian military foreign intelligence service, GRU’s unit 74455, sometimes known in the West as ‘Sandworm’ or ‘VoodooBear’. The attacks are said to have been made in retaliation for Russia’s being banned from the Olympics as punishment for endorsing doping as a standard practice. Six members of this unit have been charged by the USA with a variety of crimes related to their cyberactivities, including development of the NotPetya ransomware malware, described by an American security official as, “the most disruptive and destructive series of computer attacks ever attributed to a single group”.
Figure 1 Ransomware screen (https://upload.wikimedia.org/wikipedia/commons/5/58/PetyaA.jpg)
But wait, there’s more… British cybersecurity has uncovered activity by the same GRU unit to reconnoitre the organisers, logistics services, and sponsors of the Tokyo Summer Olympics. According to the UK’s Foreign Secretary, “The GRU’s actions against the Olympic and Paralympic Games are cynical and reckless. We condemn them in the strongest possible terms. The UK will continue to work with our allies to call out and counter future malicious cyberattacks.”
John Douglas, Technical Director of First Response, comments, “Such probing and reconnaissance of organisations, which may appear at first sight to be secondary targets, such as sponsors of the Games, often precede the actual attacks through these weaker attack points to the main target, which in this case would be the systems which actually run the Olympic Games. With these systems all interconnected, it’s important to realise that everyone everywhere is a potential target.”
Contact First Response’s cybersecurity teams for an appraisal of your cybersecurity, and ways in which it may be strengthened against attacks, no matter from where they originate.