Thieves operate all year round, of course, but Christmas is a wonderful season for them. While for most of us, it is a season of giving, for these...


Thieves operate all year round, of course, but Christmas is a wonderful season for them. While for most of us, it is a season of giving, for these...
Two-factor authentication (TFA) is now a standard part of our online life. We log onto a service, or initiate an online transaction, and just to...
The attackers – who are they? One of the first questions that may be asked is, "Who is doing this?". Analysis within the malicious code...
Every day, many businesses and organisations find their operations grinding to a painful halt as a result of an attack by threat actors deploying...
Maybe the camera doesn't know, but the phone might... The power of the handheld computers, aka smartphones, that most of us carry around with us,...

First Response Technical Director, John Douglas, talks about the 2019 Nuix Insider Conference and excitement about the Nuix partner portal....
And it’s still a potential open door for bad actors Click here to play the XP startup sound! Most people who were alive at the time can remember...

Messaging service can act as gateway to turn phones into bugging devices Although this popular messaging service, owned and operated by Facebook, is...
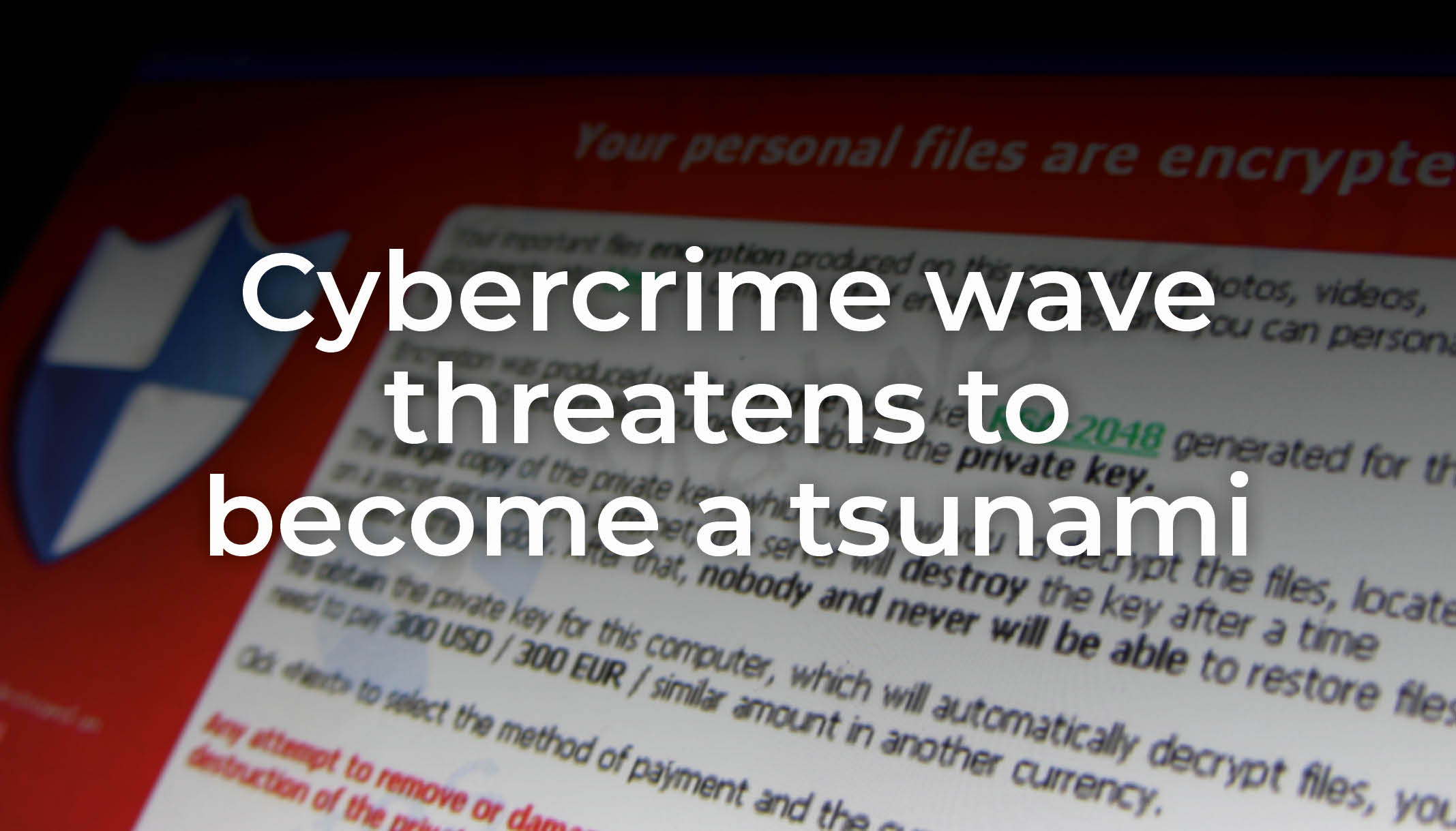
If you’re not already a target – the odds are that you soon will be Cybercrime is big business – the average cost to a business of an attack...