With cloud applications, services and infrastructure becoming the centre of organisations across the world, enabling access whilst safeguarding data is more important than ever. Security Service Edge (SSE) solutions enable organisations to greatly enhance cloud data security and help ensure compliance with regulations.
What is Security Service Edge
Security Service Edge (SSE) is a term defined by Gartner, with Security Service Edge solutions providing a broad set of features to secure access to and usage of, the web, cloud services and private applications.
Historically secure web gateways (SWG), cloud access security brokers (CASB) and remote browser isolation (RBI) solutions have been developed in isolation from one another. However, Gartner now recommends looking at vendors that have consolidated CASB, SWG, RBI and zero trust network access to a single SSE solution.
Consolidation of these capabilities is expected to create opportunities for organisations to improve their agility and ability to prevent, detect and respond to cyber threats
Gartner Security Service Edge – Critical Capabilities
Gartner has identified critical capabilities for SSE solutions including access control, threat protection, data security, security monitoring, and acceptable-use control enforced by network-based and API-based integration.
Critical Capabilities:
- Secure Web and Cloud Usage
- Detect and Mitigate Threats
- Connect and Secure Remote Workers
- Identify and Protect Sensitive Information
Who Are Lookout
Formed in 2007, Lookout first provided mobile threat defence solutions for AndroidOS, and Apple iOS.
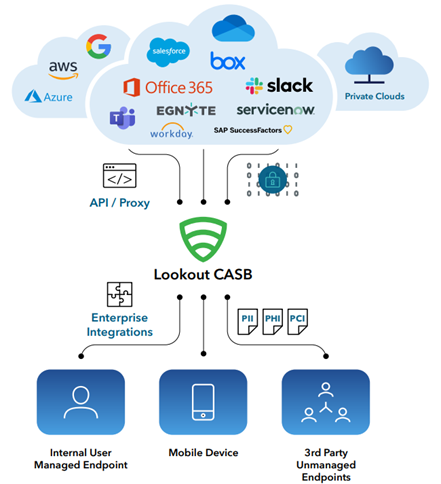
In 2021, Lookout acquired CipherCloud, a CASB+ platform which shared features like other major cloud application security brokers: data protection, adaptive access control, threat protection and centralized compliance capabilities across different SaaS and IaaS clouds.
This acquisition led Lookout to transform their offering into an integrated endpoint-to-cloud, cloud-delivered security platform.
Lookout’s Integrated Platform
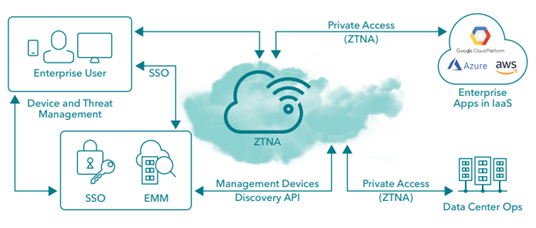
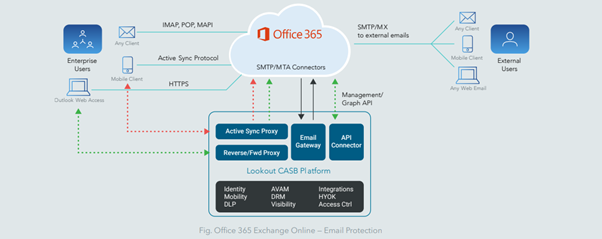
Prior to the acquisition CipherCloud had natively developed and pioneered delivery of cloud security controls to businesses. And since the acquisition the company has been further innovating solutions that span several categories, including CASB, ZTNA, SWG and Data Loss Prevention (DLP). Together these solutions deliver comprehensive visibility, data security, threat protection, and compliance for cloud-based applications.
With Lookout being a leader in mobile endpoint security, and with more mobile applications connecting to the cloud than ever, the next logical step was an integration to Lookout’s Mobile Threat Defence solution.
Lookout And SSE Critical Capabilities
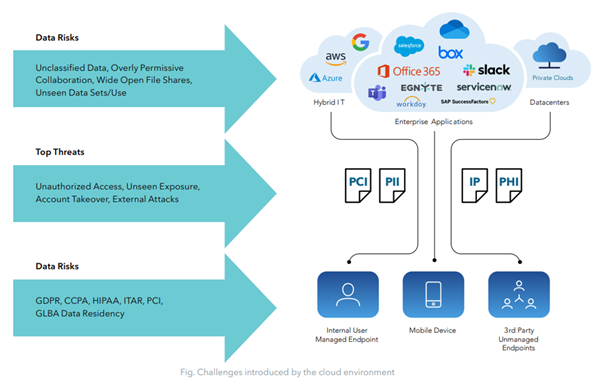
With the rapid adoption of cloud applications, shift to remote working, the amount of data transitioning out of the corporate data centre into the cloud, and with more traffic flowing to public cloud services, there is a greater need for endpoint-to-cloud security.
Lookout scored in the Top 3 across all four SSE use cases defined by Gartner. With Gartner stating “Clients looking for a comprehensive SSE solution should consider Lookout.”
Key Points To Note From The Gartner SSE Report
- Lookout’s policy engine and UI is unified and easy to access across SWG, CASB and ZTNA
- Day-to-day operations of the platform are straightforward
- Reporting is included
- The mobile threat defence product set is fully integrated to the console
- DLP and RBI are tightly integrated and feature advanced data security controls
- Endpoint coverage and detection of sensitive data transfers from the Common Internet File System (CIFS) to and from private, cloud and web channels, without requiring a separate DLP module.
- The ability to tokenize data, add watermarks and apply classification labels ingested from Azure Information Protection (AIP) and Titus
- The interface is well laid out, making investigations and general operational tasks practical
- Excellent support and management capability for Cloud Security Posture Management, SaaS Security Posture Management and the ability to govern Infrastructure as a Service
How Can Lookout Help With Cloud Data Security
DLP is critical to ensure remote workers are productive, that data is protected and that the organisation is staying compliant to regulations.
By using modern, cloud-delivered DLP, organisations can configure remediation policies based on the context of access and the context by which the exchange occurs. Lookout can efficiently identify the types of data you own across your entire infrastructure – whether it resides in data centres, on private clouds, or in SaaS apps. It can then enforce granular policies to block intentional and unintentional threats, such as malicious insiders or compromised accounts that are a potential data loss incident.
Compliance With Industry And Government Regulations
By using Lookout’s DLP engine, data can be isolated, allowing both private and public-sector organisations to safeguard sensitive personal data, and providing the ability to securely use public and private cloud.
Protecting proprietary information
Cyber threat actors may try to steal data, either for corporate or nation state espionage, or to inflict financial and reputational damage on an organisation. Stolen data may be resold or leaked on the dark web causing loss of competitive advantage and trade secrets, some threat actors may also demand a ransom payment for not releasing the data to the public.
Data loss prevention strategies can help keep intellectual property safe, from outside attacks and exfiltration, but also from unintentional data leaks caused by employees.
Securing proprietary information and sensitive personal information is all achievable with Lookout’s SSE and cloud data security platform.
The Lookout security policy engine is unified and easy to use. With a single place to monitor risk and enforce security policies, you can protect your data from external threats, insider threats or accidental data leakage.
The Lookout Security Platform cross references user behavior, endpoint risk posture and data sensitivity to adjust access policies in real time. You can enable the modern workforce without putting your data at risk.
Ways We Can Help:
If you are concerned about your use of cloud applications, services and infrastructure, or are interested in how cybersecurity monitoring and management could benefit your organisation, call or email us now for a discussion about your requirements for a more secure environment.
Further information on our Managed Cyber Security Services for Cloud is available here.