What is Ransomware
Ransomware is a specific type of malicious software which is used by organised cybercriminal networks to encrypt victim organisations’ critical value data as part of a ransomware campaign. The threat actors then demand a ransom to decrypt the data. Threat intelligence companies are currently tracking over 100 active ransomware groups.
First Response provides cyber incident response services and incident response for ransomware attacks, both are detailed in the sections that follow. Details of our cyber incident response plan and incident response preparations can be found here.
Successful ransomware attacks can:
- encrypt devices, servers, desktop, and laptop computers
- cause devices to become locked or unusable
- make critical value data inaccessible to the organisation
Ransomware attack groups are highly organised and have consistently developed their tactics and techniques to evade detection from cyber defences and to maximise the success of extracting ransom payments. They will usually target victims with the intent to:
- take control of the devices to attack other organisations
- obtain credentials to gain access to your organisation’s systems or services
- destroy, or encrypt your organisations backup systems
- sell or publish your stolen data on the internet
- demand a second ransom payment to prevent public release of your data
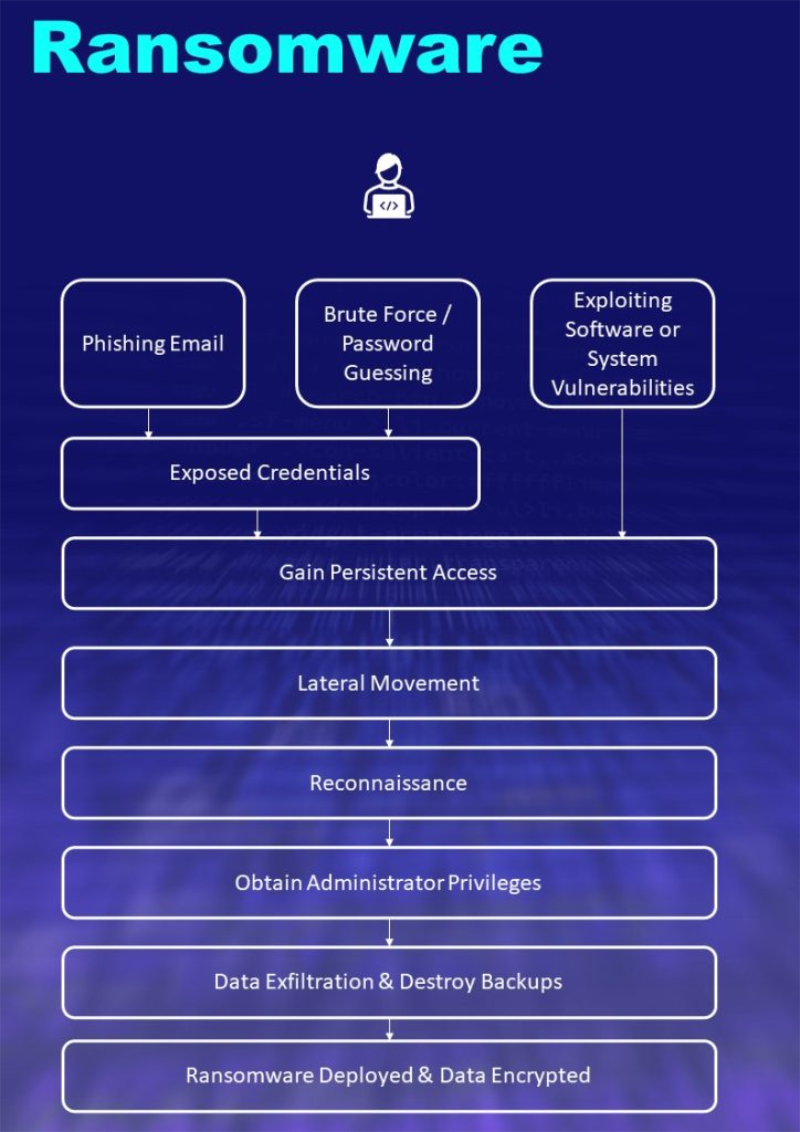
Once your computers and servers are encrypted it is often impossible to gain access to those systems without the decryption key from the attackers, or without good quality backups. The cryptography employed is highly sophisticated and cannot be brute-forced or otherwise broken – only the decryption key will recover the encrypted critical value data.
Backup policies differ across organisations and some may find that even with backups they still cannot recover their data. Often this is because the backups are either too old to recover from, it would take too long to recover, the attackers disabled/deleted/encrypted the backups, or because the backups have been otherwise compromised during the attack and are unusable or unreliable.
Once the attackers have completed their attack they will usually request that the victim contact them via the dark web, they will then try to begin negotiations for the decryption key. It is important to note that even after paying the ransom there is no guarantee the decryption key will work, or that you will recover your data. This is why it is important for organisations to implement a robust security strategy to deal with the threat of ransomware beforehand.
Types of organisations ransomware groups target
All organisations are potential targets for ransomware attack groups. Some groups have stated publicly that they will not target non-profits, schools, or hospitals. Unfortunately, these types of organisations may still be a target for other less scrupulous attack groups. Recent ransomware examples in the UK include M&S and Jaguar Land Rover.
The types of services and systems ransomware attackers target
- Cloud applications and cloud services
- File servers and file shares
- Line of Business applications
- ERP and CRM systems
- Telephony/VOIP
- Other core IT infrastructure such as Domain Controllers and Active Directory
Double extortion
Ransomware attack groups are constantly changing their approaches and tactics to ensure maximum damage to organisations. Over the last few years there has been an increase in the trend for these groups to steal confidential information and data from an organisation prior to them encrypting systems and services. The threat actor will demand a ransom payment, usually in Bitcoin to decrypt the organisations data. Several weeks later they then threaten to leak this information if a second ransom isn’t paid.
Organisations that do pay a ransom not only have no guarantee that the decryptor will work, or that the files won’t be publicly leaked, but also go on a ‘suckers list’ that is shared with other ransomware gangs encouraging them to execute follow-up attacks.
When you need an incident response team
Attackers will move across a computer network conducting reconnaissance and gathering intelligence as they move. The initial phases of an attack may last a few weeks or days, but the last phase of the attack can happen very quickly. Once the attacker has disabled an organisations defences and the encryption process has started, an organisations IT system could be encrypted in a matter of hours. This is often done during long weekends or other holidays to ensure the encryption has time to complete before being discovered.
This can make it very difficult for IT and security teams to respond as they are often under extreme pressure from the executive team to bring systems back online.
If the IT or security team is inexperienced when dealing with ransomware incidents or if there are complications during the recovery process, it is usually best to call in an experienced incident response team. This is to ensure the organisations IT systems are restored effectively and efficiently.
In some scenarios IT teams have inadvertently restored from backups before the attack has completed or the attackers have been expelled from the network which has then led to the backups being compromised. It is also possible that systems are brought back online whilst the attacker is still inside the network, or that the original attack vector that the attacker took to compromise the system hasn’t been remediated; meaning they could return to it at a later date.
It may also be the case that the organisation doesn’t have the requisite technology in place to conduct a forensic investigation to identify ‘patient zero’ or to thoroughly complete the remediation process.
Common problems responding to ransomware attacks
With ransomware incidents, we often see that companies don’t communicate well. This is not surprising, as this may be the first time IT staff and executives have had to handle an incident of this type. Clear, straightforward communication is essential when dealing with any incident, but with a ransomware attack it is especially important.
Another common misconception we see fairly regularly, is the expectation that a cyber incident or ransomware attack is solely an IT problem and that “we just need the IT team to deal with it.” Because of the potential financial, operational, legal and reputational ramifications, it is important that the composition of the core incident response team focusses on senior management to ensure that the decision-making process remains swift and that decisions are not deferred or delayed by those lacking the appropriate authority.
Representative Composition of the Core Incident Response Team:
- Board Representative or CEO/CFO
- Technical Services Director
- Head of Corporate Communications
- Head of Legal & Compliance
- Head of Internal Audit
- Head of IT & Cybersecurity
- Head of Human Resources
Detection and analysis
Once an incident has been detected it should be assessed and categorised according to the organisation’s incident response framework.
Organisations without a written and documented cybersecurity incident response plan will most likely lack a process for reporting, assessing and triaging potential incidents. However, if you decide to engage with an external incident response team, there is specific data and information around the incident that should be captured, including (but not limited to):
- What type of attack is it (validate whether it is actually ransomware and not phishing or other malware)
- Which systems are affected (i.e. which applications, networks, servers and services are affected)
- What are the indicators of compromise (files, processes, network connections)
- What data is affected (e.g., file types, department or group, affected software)
- How critical is the data
- How sensitive is the data
- What is the regulatory status of the data (i.e. PCI, PII, PHI)
Network diagrams and supporting information should be prepared, detailing:
- Internet gateways
- IP address ranges and any separate VLANs
- remote access
- key systems (file servers, platforms, domain controllers, webservers)
- physical locations of servers
It is important to document all security appliances and software which could be useful during the response to the incident.
Regulatory implications
If you’ve discovered a personal data breach likely to result in a risk to the rights and freedoms of individuals, you must report it within 72 hours under the UK GDPR & DPA to the Information Commissioner’s Office (ICO). You may also need to report incidents to stakeholders, such as regulators, insurers, customers or partners.
Guidelines
The US Cybersecurity & Infrastructure Agency has published joint guidelines with the UK National Cybersecurity Centre, detailing Technical Approaches to Uncovering and Remediating Malicious Activity
If your team lacks the necessary experience in responding to ransomware or any other sophisticated cyber-attack, you should seek guidance from external specialists.
First Response has experience working on over 200 cyber incidents, including large and small ransomware attacks, across public and private sector organisations.
How we can help
If you have a cybersecurity incident, believe you are under attack or have been compromised, then call us immediately for assistance on +4420 7193 4905 or email us as incident [at] first-response.co.uk.
More information on the cyber incident response services we provide is available here.
We also provide a pro-active managed detection and response service with Microsoft 365 Defender XDR and Cynet, details are available here.
Common misconceptions about ransomware:

