Welcome to First Response
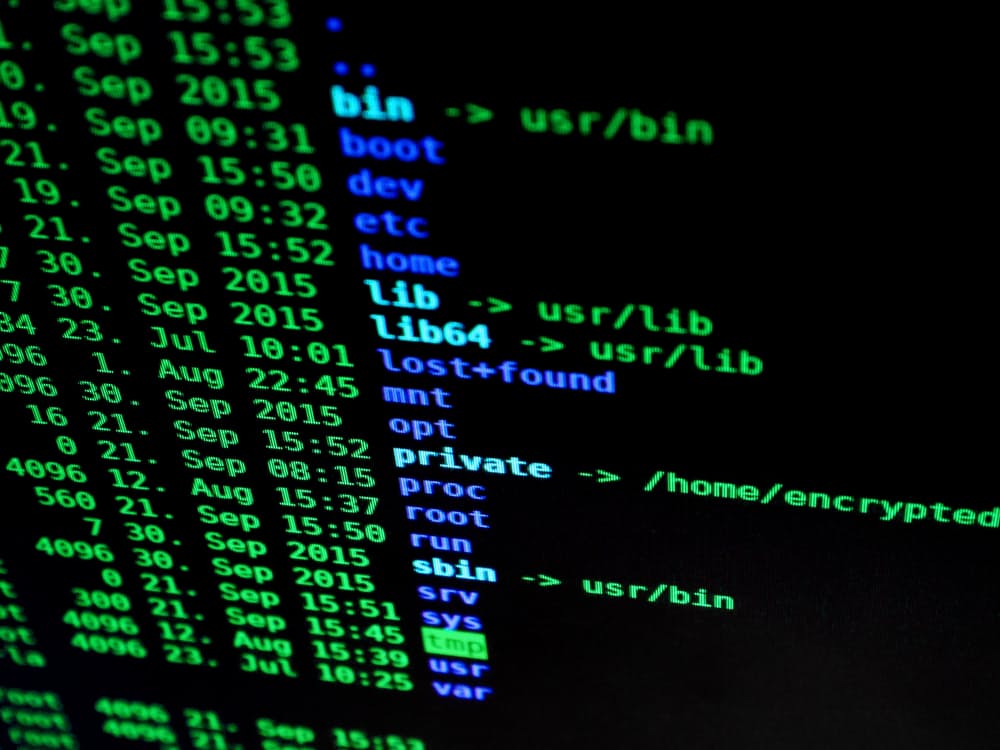
First Response is a specialist cybersecurity, digital forensics and incident response company that helps organisations navigate the complex issues surrounding systems breaches, server compromises and data loss. We work with a wide variety of clients including banks, law firms, energy & manufacturing companies and public sector bodies.
We are headquartered in London with offices in Manchester and Rome, from where we assist our clients around the world.
Cybersecurity & Incident Response Specialists
If your company has suffered a data breach or network compromise; from ransomware to data theft, we have the skills and experience to help you deal with attacks on your computer systems and data.
Very few organisations have the technical skills in-house to deal with sophisticated multi-tier attacks, and often the well-intentioned but clumsy responses by internal teams under pressure to resolve an issue will overwrite critical evidence and greatly reduce the chances of a successful outcome.
We deal with data loss events every day and have learned through the mistakes of others so you don’t have to. We can resolve a current incident or help you to better prepare and deal with one in the future.
First Response is a Cybersecurity and Incident Response company, offering tailored services in response to network breaches. We provide a range of services around computer-based IT and network investigations and litigation support, to more specialist areas:
- cybercrime training
- malware reverse engineering
- cyber readiness planning
- establishing an incident response framework

Cyber Incident Response

Digital Forensic Investigations

Managed Cybersecurity Services

Managed Detection Response for Microsoft Defender
“First Response identified the source and extent of the breach and provided invaluable guidance on how to deal with it. They helped us significantly reduce the impact on our company.”
Blog Articles
Incident Response for Ransomware
What is Ransomware Ransomware is a specific type of malicious software which is...
Cyber Security Incident Response Services
Cyber incident response or cyber security incident response services may be called on...
Cyber Security Incident Response – Ransomware Attack
Our cyber security incident response team works with clients across the globe, helping...